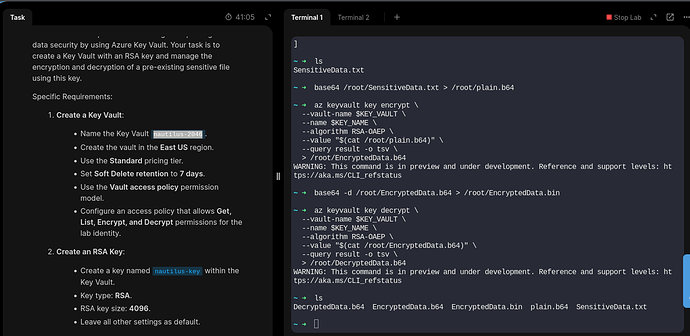
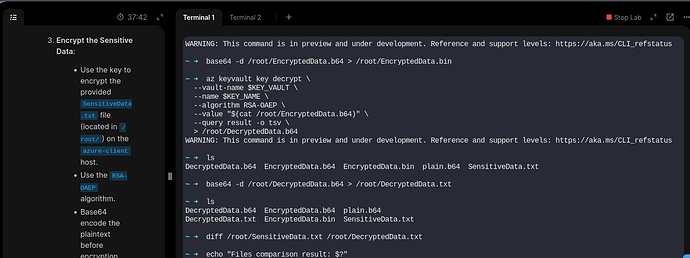
All tasks completed with azcli
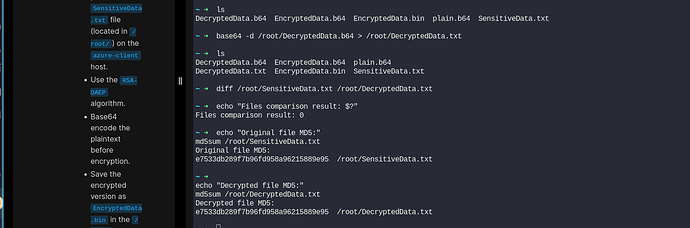
file crypted and decrytped successfully. check done wit diff command and echo “Files comparison result: $?”.
BUt finaly, i had the message below and then they said I’am not good.
============================= test session starts ==============================
platform linux – Python 3.10.15, pytest-8.3.4, pluggy-1.5.0
rootdir: /usr/share
plugins: testinfra-10.1.1
collected 1 item
…/usr/share/test.py F [100%]
=================================== FAILURES ===================================
_________________________ test_key_vault_configuration _________________________
def test_key_vault_configuration():
host = testinfra.get_host("local://")
# Step 1: Verify Key Vault and Key exist
key_vault_name = 'xfusion-7656'
key_name = 'xfusion-key'
# Check if Key Vault exists
key_vault_check = host.run(f"az keyvault show --name {key_vault_name} --query 'name' -o tsv")
assert key_vault_check.rc == 0, f"Key Vault '{key_vault_name}' not found."
# Check if Key exists in the Key Vault
key_check = host.run(f"az keyvault key show --vault-name {key_vault_name} --name {key_name} --query 'key.kid' -o tsv")
assert key_check.rc == 0, f"Key '{key_name}' not found in Key Vault '{key_vault_name}'."
# Step 2: Perform decryption using the Key Vault key and verify that decryption is successful
encrypted_file = "/root/EncryptedData.bin"
decrypted_file = "/tmp/DecryptedData.txt"
# Check if the encrypted file exists
file = host.file(encrypted_file)
assert file.exists, f"File '{encrypted_file}' doesn't exist; it seems you didn't encrypt the '/root/SensitiveData.txt' file."
# Read the encrypted file content as binary
with open(encrypted_file, "rb") as f:
encrypted_data = f.read()
# Define RSA-2048 modulus limit (256 bytes max)
RSA_MAX_LENGTH = 256
# Check if encrypted data exceeds RSA limit
if len(encrypted_data) > RSA_MAX_LENGTH:
print("Encrypted data exceeds RSA limit. Assuming it's base64-encoded and decoding first.")
encrypted_data = base64.b64decode(encrypted_data)
/usr/share/test.py:38:
s = b’\x13\xa0\xe5\xcf\x89\x10\xe6z~\x12\xdd~\x009|\x8e\x8e\xe7\xe6\xfc\C.\xe3\xcc\x05\K"d\xaf\xe5\xe3/\x93v\x1aa\xd9\x9…xd2F\xe0YT;\x1c\xc0\xfb\xde\x92\1m\n\xdfIg\x9c\x8f\xce\xaa{1\x9f\xe3k\xf3Q\xf9\r\xe6\xd9\x02\x04L\xb7\x00\xad\xf8\x93’
altchars = None, validate = False
def b64decode(s, altchars=None, validate=False):
"""Decode the Base64 encoded bytes-like object or ASCII string s.
Optional altchars must be a bytes-like object or ASCII string of length 2
which specifies the alternative alphabet used instead of the '+' and '/'
characters.
The result is returned as a bytes object. A binascii.Error is raised if
s is incorrectly padded.
If validate is False (the default), characters that are neither in the
normal base-64 alphabet nor the alternative alphabet are discarded prior
to the padding check. If validate is True, these non-alphabet characters
in the input result in a binascii.Error.
"""
s = _bytes_from_decode_data(s)
if altchars is not None:
altchars = _bytes_from_decode_data(altchars)
assert len(altchars) == 2, repr(altchars)
s = s.translate(bytes.maketrans(altchars, b'+/'))
if validate and not re.fullmatch(b'[A-Za-z0-9+/]*={0,2}', s):
raise binascii.Error('Non-base64 digit found')
return binascii.a2b_base64(s)
E binascii.Error: Incorrect padding
/usr/local/lib/python3.10/base64.py:87: Error
----------------------------- Captured stdout call -----------------------------
Encrypted data exceeds RSA limit. Assuming it’s base64-encoded and decoding first.
=========================== short test summary info ============================
FAILED …/usr/share/test.py::test_key_vault_configuration - binascii.Error: I…
============================== 1 failed in 4.63s ===============================