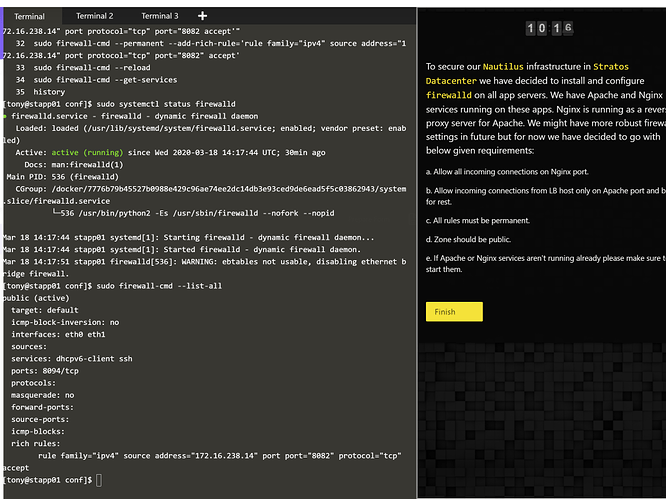
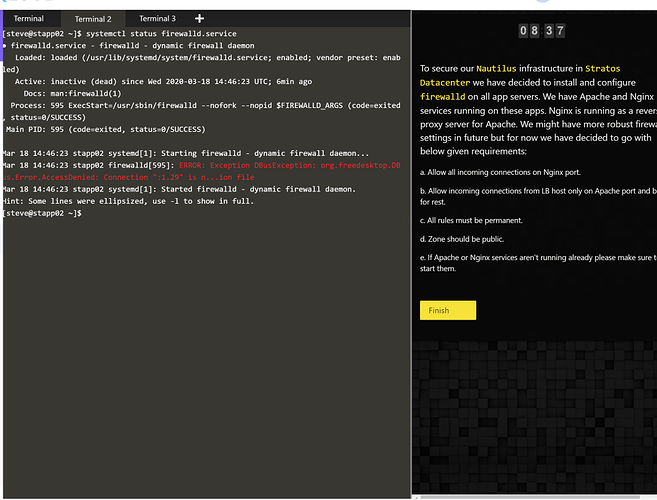
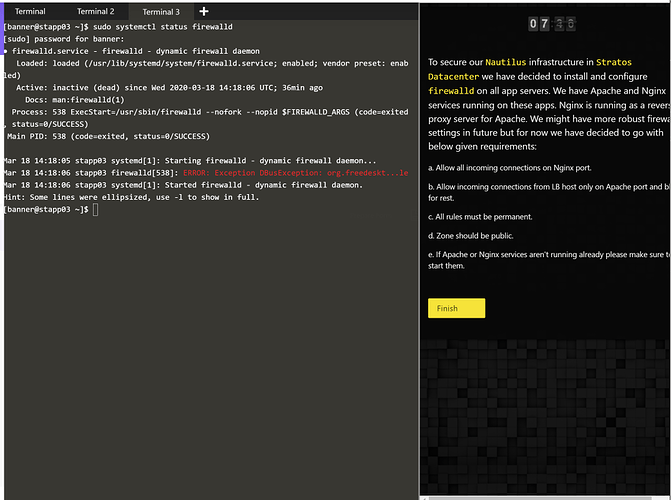
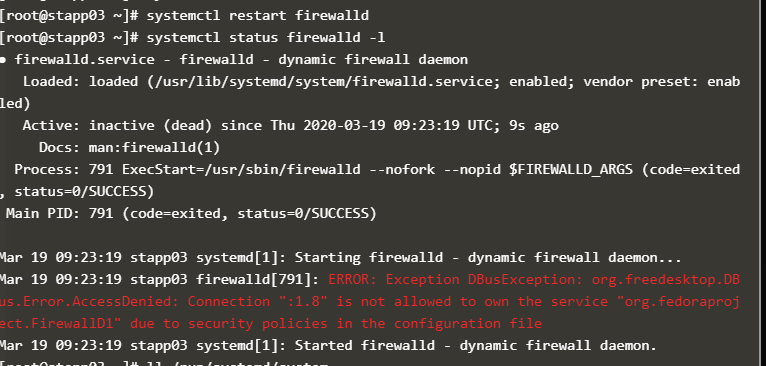
I had some issues starting firewalld on the 2nd and 3rd app server, which prevented me from completing this task. I’m going to include in screenshots the errors I got on app servers 2 and 3. I also want to show I was able to get the firewall rules setup on app server 1. I’m hoping I can get the credit for this task.
Please give it another try and let us know if you face same issues, also please try to share exact steps you take to solve this task.
Hi,
I had to delete the package polkit, then restart the services dbus, after this two action everything work fine.
Regards,
I am having similar issue…
On 2 app servers the service firewalld is running fine but the 3rd app server its not running. I tried to update and reinstall the packages but doesnt work. Can you please assist.
this is what i did but my job still failed. ![]()
thor@jump_host /$
thor@jump_host /$ ssh [email protected]
The authenticity of host '172.16.238.11 (172.16.238.11)' can't be established.
ECDSA key fingerprint is SHA256:SySamszyWhhLGFiybhGBqfrr8g55wS/3e37ZpBOvICs.
ECDSA key fingerprint is MD5:6d:31:18:2a:f9:07:f3:29:dd:0a:d3:1f:6e:04:0a:db.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '172.16.238.11' (ECDSA) to the list of known hosts.
[email protected]'s password:
[steve@stapp02 ~]$ sudo su -
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
[sudo] password for steve:
[root@stapp02 ~]# yum install firewalld
Loaded plugins: fastestmirror, ovl
Determining fastest mirrors
epel/x86_64/metalink | 22 kB 00:00:00
* base: centosmirror.netcup.net
* epel: ftp.plusline.net
* extras: ftp.plusline.net
* remi-php72: remi.mirror.karneval.cz
* remi-safe: remi.mirror.karneval.cz
* updates: ftp.rz.uni-frankfurt.de
base | 3.6 kB 00:00:00
epel | 5.3 kB 00:00:00
extras | 2.9 kB 00:00:00
remi-php72 | 3.0 kB 00:00:00
remi-safe | 3.0 kB 00:00:00
updates | 2.9 kB 00:00:00
(1/7): extras/7/x86_64/primary_db | 164 kB 00:00:00
(2/7): epel/x86_64/group_gz | 95 kB 00:00:01
(3/7): epel/x86_64/updateinfo | 1.0 MB 00:00:01
(4/7): epel/x86_64/primary_db | 6.7 MB 00:00:01
(5/7): updates/7/x86_64/primary_db | 7.5 MB 00:00:00
(6/7): remi-php72/primary_db | 234 kB 00:00:01
(7/7): remi-safe/primary_db | 1.7 MB 00:00:01
Resolving Dependencies
--> Running transaction check
---> Package firewalld.noarch 0:0.6.3-2.el7_7.4 will be installed
--> Processing Dependency: python-firewall = 0.6.3-2.el7_7.4 for package: firewalld-0.6.3-2.el7_7.4.noarch
--> Processing Dependency: firewalld-filesystem = 0.6.3-2.el7_7.4 for package: firewalld-0.6.3-2.el7_7.4.noarch
--> Processing Dependency: ipset for package: firewalld-0.6.3-2.el7_7.4.noarch
--> Processing Dependency: ebtables for package: firewalld-0.6.3-2.el7_7.4.noarch
--> Running transaction check
---> Package ebtables.x86_64 0:2.0.10-16.el7 will be installed
---> Package firewalld-filesystem.noarch 0:0.6.3-2.el7_7.4 will be installed
---> Package ipset.x86_64 0:7.1-1.el7 will be installed
--> Processing Dependency: ipset-libs(x86-64) = 7.1-1.el7 for package: ipset-7.1-1.el7.x86_64
--> Processing Dependency: libipset.so.13(LIBIPSET_4.8)(64bit) for package: ipset-7.1-1.el7.x86_64
--> Processing Dependency: libipset.so.13(LIBIPSET_2.0)(64bit) for package: ipset-7.1-1.el7.x86_64
--> Processing Dependency: libipset.so.13()(64bit) for package: ipset-7.1-1.el7.x86_64
---> Package python-firewall.noarch 0:0.6.3-2.el7_7.4 will be installed
--> Processing Dependency: python-slip-dbus for package: python-firewall-0.6.3-2.el7_7.4.noarch
--> Processing Dependency: python-decorator for package: python-firewall-0.6.3-2.el7_7.4.noarch
--> Running transaction check
---> Package ipset-libs.x86_64 0:7.1-1.el7 will be installed
---> Package python-decorator.noarch 0:3.4.0-3.el7 will be installed
---> Package python-slip-dbus.noarch 0:0.4.0-4.el7 will be installed
--> Processing Dependency: python-slip = 0.4.0-4.el7 for package: python-slip-dbus-0.4.0-4.el7.noarch
--> Running transaction check
---> Package python-slip.noarch 0:0.4.0-4.el7 will be installed
--> Processing Dependency: libselinux-python for package: python-slip-0.4.0-4.el7.noarch
--> Running transaction check
---> Package libselinux-python.x86_64 0:2.5-14.1.el7 will be installed
--> Finished Dependency Resolution
Dependencies Resolved
===================================================================================================================================================================================
Package Arch Version Repository Size
===================================================================================================================================================================================
Installing:
firewalld noarch 0.6.3-2.el7_7.4 updates 441 k
Installing for dependencies:
ebtables x86_64 2.0.10-16.el7 base 123 k
firewalld-filesystem noarch 0.6.3-2.el7_7.4 updates 50 k
ipset x86_64 7.1-1.el7 base 39 k
ipset-libs x86_64 7.1-1.el7 base 64 k
libselinux-python x86_64 2.5-14.1.el7 base 235 k
python-decorator noarch 3.4.0-3.el7 base 27 k
python-firewall noarch 0.6.3-2.el7_7.4 updates 353 k
python-slip noarch 0.4.0-4.el7 base 31 k
python-slip-dbus noarch 0.4.0-4.el7 base 32 k
Transaction Summary
===================================================================================================================================================================================
Install 1 Package (+9 Dependent packages)
Total download size: 1.4 M
Installed size: 5.1 M
Is this ok [y/d/N]: y
Downloading packages:
(1/10): ebtables-2.0.10-16.el7.x86_64.rpm | 123 kB 00:00:00
(2/10): libselinux-python-2.5-14.1.el7.x86_64.rpm | 235 kB 00:00:00
(3/10): python-decorator-3.4.0-3.el7.noarch.rpm | 27 kB 00:00:00
(4/10): firewalld-filesystem-0.6.3-2.el7_7.4.noarch.rpm | 50 kB 00:00:00
(5/10): python-slip-0.4.0-4.el7.noarch.rpm | 31 kB 00:00:00
(6/10): python-firewall-0.6.3-2.el7_7.4.noarch.rpm | 353 kB 00:00:00
(7/10): python-slip-dbus-0.4.0-4.el7.noarch.rpm | 32 kB 00:00:00
(8/10): ipset-7.1-1.el7.x86_64.rpm | 39 kB 00:00:00
(9/10): ipset-libs-7.1-1.el7.x86_64.rpm | 64 kB 00:00:00
(10/10): firewalld-0.6.3-2.el7_7.4.noarch.rpm | 441 kB 00:00:01
--------------------------------------------------------------------------------------------------------------
Total 1.1 MB/s | 1.4 MB 00:00:01
Running transaction check
Running transaction test
Transaction test succeeded
Running transaction
Installing : python-decorator-3.4.0-3.el7.noarch 1/10
Installing : ebtables-2.0.10-16.el7.x86_64 2/10
Installing : ipset-libs-7.1-1.el7.x86_64 3/10
Installing : ipset-7.1-1.el7.x86_64 4/10
Installing : libselinux-python-2.5-14.1.el7.x86_64 5/10
Installing : python-slip-0.4.0-4.el7.noarch 6/10
Installing : python-slip-dbus-0.4.0-4.el7.noarch 7/10
Installing : python-firewall-0.6.3-2.el7_7.4.noarch 8/10
Installing : firewalld-filesystem-0.6.3-2.el7_7.4.noarch 9/10
Installing : firewalld-0.6.3-2.el7_7.4.noarch 10/10
Verifying : firewalld-filesystem-0.6.3-2.el7_7.4.noarch 1/10
Verifying : ipset-7.1-1.el7.x86_64 2/10
Verifying : python-firewall-0.6.3-2.el7_7.4.noarch 3/10
Verifying : libselinux-python-2.5-14.1.el7.x86_64 4/10
Verifying : python-slip-0.4.0-4.el7.noarch 5/10
Verifying : firewalld-0.6.3-2.el7_7.4.noarch 6/10
Verifying : python-slip-dbus-0.4.0-4.el7.noarch 7/10
Verifying : python-decorator-3.4.0-3.el7.noarch 8/10
Verifying : ipset-libs-7.1-1.el7.x86_64 9/10
Verifying : ebtables-2.0.10-16.el7.x86_64 10/10
Installed:
firewalld.noarch 0:0.6.3-2.el7_7.4
Dependency Installed:
ebtables.x86_64 0:2.0.10-16.el7 firewalld-filesystem.noarch 0:0.6.3-2.el7_7.4
ipset.x86_64 0:7.1-1.el7 ipset-libs.x86_64 0:7.1-1.el7
libselinux-python.x86_64 0:2.5-14.1.el7 python-decorator.noarch 0:3.4.0-3.el7
python-firewall.noarch 0:0.6.3-2.el7_7.4 python-slip.noarch 0:0.4.0-4.el7
python-slip-dbus.noarch 0:0.4.0-4.el7
Complete!
[root@stapp02 ~]# systemctl restart dbus
[root@stapp02 ~]# sudo systemctl restart firewalld
[root@stapp02 ~]# sudo firewall-cmd --state
running
[root@stapp02 ~]# sudo systemctl status nginx
● nginx.service - The nginx HTTP and reverse proxy server
Loaded: loaded (/usr/lib/systemd/system/nginx.service; disabled; vendor preset: disabled)
Active: active (running) since Thu 2020-03-19 13:41:42 UTC; 8min ago
Main PID: 284 (nginx)
CGroup: /docker/e62e26af05eadb83d483218a9c163c62e12a04f7f14612d0a22ade752562849c/system.slice/nginx.service
├─284 nginx: master process /usr/sbin/nginx
├─285 nginx: worker process
└─286 nginx: worker process
Mar 19 13:41:42 stapp02 systemd[1]: Starting The nginx HTTP and reverse proxy server...
Mar 19 13:41:42 stapp02 nginx[282]: nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
Mar 19 13:41:42 stapp02 nginx[282]: nginx: configuration file /etc/nginx/nginx.conf test is successful
Mar 19 13:41:42 stapp02 systemd[1]: Started The nginx HTTP and reverse proxy server.
[root@stapp02 ~]# sudo systemctl status httpd
● httpd.service - The Apache HTTP Server
Loaded: loaded (/usr/lib/systemd/system/httpd.service; disabled; vendor preset: disabled)
Active: active (running) since Thu 2020-03-19 13:41:42 UTC; 9min ago
Docs: man:httpd(8)
man:apachectl(8)
Main PID: 266 (httpd)
Status: "Total requests: 0; Current requests/sec: 0; Current traffic: 0 B/sec"
CGroup: /docker/e62e26af05eadb83d483218a9c163c62e12a04f7f14612d0a22ade752562849c/system.slice/httpd.service
├─266 /usr/sbin/httpd -DFOREGROUND
├─268 /usr/sbin/httpd -DFOREGROUND
├─269 /usr/sbin/httpd -DFOREGROUND
├─270 /usr/sbin/httpd -DFOREGROUND
├─271 /usr/sbin/httpd -DFOREGROUND
└─272 /usr/sbin/httpd -DFOREGROUND
Mar 19 13:41:42 stapp02 systemd[1]: Starting The Apache HTTP Server...
Mar 19 13:41:42 stapp02 httpd[266]: AH00558: httpd: Could not reliably determine the server's fully qualified domain name, using 172.16.238.11. Set the 'ServerName'...this message
Mar 19 13:41:42 stapp02 systemd[1]: Started The Apache HTTP Server.
Hint: Some lines were ellipsized, use -l to show in full.
[root@stapp02 ~]# sudo firewall-cmd --zone=public --permanent --add-port=8092/tcp
success
[root@stapp02 ~]# sudo firewall-cmd --zone=public --permanent --add-service=https
success
[root@stapp02 ~]# sudo firewall-cmd --zone=public --permanent --add-service=http
success
[root@stapp02 ~]# sudo firewall-cmd --permanent --zone=public --add-rich-rule='rule family=ipv4 source address=172.16.238.14 port protocol=tcp port=80 accept'
success
[root@stapp02 ~]# sudo firewall-cmd --reload
success
[root@stapp02 ~]# sudo firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: dhcpv6-client http https ssh
ports: 8092/tcp
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
rule family="ipv4" source address="172.16.238.14" port port="80" protocol="tcp" accept
what is the task? Can i help you?
I faced the same problem, and I solved it by issuing the following commands:
sudo systemctl restart dbus
sudo systemctl reestart firewalld
Hi,
You did the task with the port 80 for apache, which is not correct, you must verify the actual working port on httpd conf file.
Hi informixids , can you help me with the same task ? Actually when I determined the ports which these services are using and added them in firewalld still i get 403 forbidden , when I curl nginx port. Please help.